A few months ago, I acquired several AI accelerators – Habana Labs Goya, the first...
Read MoreWhen Availability is top priority
IT and OT Cyber Security
Although IT (Information Technology) and OT (Operational Technology) originate from distinct domains, their convergence is becoming increasingly evident. As industrial environments become more connected, the boundaries between these two worlds are blurring — introducing new cybersecurity challenges. Bridging IT and OT security is essential to ensure operational continuity, data integrity, and protection against emerging threats targeting critical infrastructure.
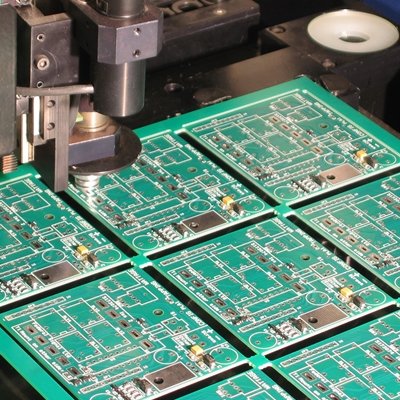
OT Security
Advanced OT Cyber Security Solutions for Industrial Environments
In the realm of Operational Technology, where industrial processes and critical infrastructures intersect, ensuring the security and continuity of operations is paramount. Our specialized OT cybersecurity services are designed to protect your industrial systems, machinery, and processes from cyber threats, allowing you to focus on driving efficiency and innovation.

IT Security
Comprehensive IT Cyber Security Services
In today’s digital age, safeguarding sensitive data and ensuring the uninterrupted operation of your business is paramount. Our IT cybersecurity services are tailored to protect your organization from evolving cyber threats, providing robust defenses and peace of mind.
We are part of the CYB3R ALLIANCE
Our Blog
Check our latest articles about IT, OT and Cyber Security
Building the Perfect AI Cluster: A Chassis Challenge
Recently, I was diving into a project focused on building a custom AI cluster, which...
Read MoreIs Governance in OT Necessary? InfraSec 2025
📅 It’s March, and the excitement from the 9th edition of #InfraSECForum2025 🛡️ has settled,...
Read MoreIntel Xeon PHI 7220p – Forgotten Accelerator
A Journey Through Exotic Systems and Hardware It’s no secret that I enjoy exploring exotic...
Read MoreFollow the latest Cyber Security news
Stay ahead with real-time updates, expert insights, and critical threat intelligence.
- Cybersecurity Stars Awards 2026: Winners Announced Across 95 Categories
Most good security work is invisible by design. Today is the exception. The 2026 Cybersecurity Stars Awards winners are announced across 95 subcategories in four main award categories. The reason is simple. Cybersecurity is full of work that deserves recognition and rarely gets it. Products that quietly close real gaps. Teams that stop incidents nobody reads about. Companies that raise the
- ThreatsDay Bulletin: Worm Code Leaked, AI Agent Phished, Claude Action Patch + 28 New Stories
It's been one of those weeks. You expect the usual noise: recycled malware, sloppy attacks, another easy target getting hit. Instead, there's a supply chain attack kit in a public repo, a $5,000-a-month RAT that clones browsers, and research showing AI agents can be tricked into leaking real credentials. The bigger problem is how polished this all looks now. Mule networks run like SaaS.
- AI Broke Vulnerability Management. That's Why CISOs Are Moving Budget to BAS.
For thirty years, vulnerability management ran on a buffer: the months between when a vulnerability was found and when someone could figure out how to weaponize it. The solution was straightforward enough; triage by severity, schedule the fix, validate, and move on. The buffer was what made that work. Today, that buffer is gone. AI didn't make your team slower. It changed the other side of the
- OceanLotus Hits Vietnam Investors With SPECTRALVIPER in FireAnt Attack
The Vietnam-aligned threat actor known as OceanLotus has been attributed to two distinct campaigns that targeted domestic entities and stock investors with a backdoor known as SPECTRALVIPER. The campaigns involve a prolonged cyber espionage operation aimed at a Vietnamese infrastructure and transport construction corporation between mid-2024 and February 2026, as well as a supply chain attack
- GitHub to Disable npm Install Scripts by Default to Stop Supply Chain Attacks
GitHub has announced what it said are "breaking changes" coming to npm version 12, one of which turns off install scripts by default to combat software supply chain threats. The changes aim to combat attack techniques that abuse the "npm install" command to trigger the execution of malicious code using npm lifecycle hooks. "Npm install" is used to download and install all the necessary
- China-Linked JDY Botnet Expands to 1,500+ Devices for Cyber Reconnaissance
Cybersecurity researchers have warned of a "resurgence and expansion" of JDY, a covert network associated with China-nexus state-sponsored threat actors. "The JDY botnet comprises over 1,500 SOHO [small office and home office] and IoT devices and operates as a centrally controlled, high-performance scanner used to discover, fingerprint, and continuously map exposed services at scale," Lumen's
Reduce the Cyber Risk in your Company