A few months ago, I acquired several AI accelerators – Habana Labs Goya, the first...
Read MoreWhen Availability is top priority
IT and OT Cyber Security
Although IT (Information Technology) and OT (Operational Technology) originate from distinct domains, their convergence is becoming increasingly evident. As industrial environments become more connected, the boundaries between these two worlds are blurring — introducing new cybersecurity challenges. Bridging IT and OT security is essential to ensure operational continuity, data integrity, and protection against emerging threats targeting critical infrastructure.
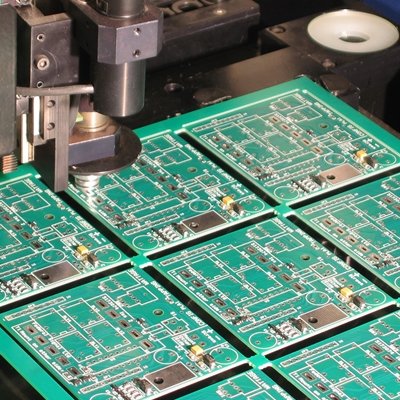
OT Security
Advanced OT Cyber Security Solutions for Industrial Environments
In the realm of Operational Technology, where industrial processes and critical infrastructures intersect, ensuring the security and continuity of operations is paramount. Our specialized OT cybersecurity services are designed to protect your industrial systems, machinery, and processes from cyber threats, allowing you to focus on driving efficiency and innovation.

IT Security
Comprehensive IT Cyber Security Services
In today’s digital age, safeguarding sensitive data and ensuring the uninterrupted operation of your business is paramount. Our IT cybersecurity services are tailored to protect your organization from evolving cyber threats, providing robust defenses and peace of mind.
We are part of the CYB3R ALLIANCE
Our Blog
Check our latest articles about IT, OT and Cyber Security
Building the Perfect AI Cluster: A Chassis Challenge
Recently, I was diving into a project focused on building a custom AI cluster, which...
Read MoreIs Governance in OT Necessary? InfraSec 2025
📅 It’s March, and the excitement from the 9th edition of #InfraSECForum2025 🛡️ has settled,...
Read MoreIntel Xeon PHI 7220p – Forgotten Accelerator
A Journey Through Exotic Systems and Hardware It’s no secret that I enjoy exploring exotic...
Read MoreFollow the latest Cyber Security news
Stay ahead with real-time updates, expert insights, and critical threat intelligence.
- Android Spyware Asin Targets Arabic Users via Fake News, PDF and War Map Apps
Arabic-speaking users have emerged as the target of a new Android spyware codenamed Asin, according to findings from ESET. The Slovakian cybersecurity company said it first detected the malware spread via multiple campaigns in early 2025, with each attack wave making use of distinct websites mimicking utilities, war-related updates, and a government news source: govlens[.]net, which
- New Threat Cluster OP-512 Targets Microsoft IIS Servers with Custom Web Shell Framework
Cybersecurity researchers have discovered a previously unreported threat cluster dubbed OP-512 (where "OP" stands for "opponent") that has been observed targeting Microsoft Internet Information Services (IIS) servers to deploy a bespoke web shell framework. ReliaQuest has assessed with moderate to high confidence that the espionage-focused activity is linked to China. "OP-512 was highly
- Only 10% of SOCs Say They’re Getting Excellent Value From AI. Here’s What the Second Wave Has to Deliver
Eighteen months ago, the AI SOC was a marketing line. Today it's a budget item. The category has crossed over from interesting to inevitable, with billions of dollars now flowing into AI-powered security operations platforms, agentic SOC tools, and AI co-pilots built into every layer of the security stack. The data shows SOCs are buying, deploying, and standing up AI capabilities at the fastest
- Hackers Exploit Critical Everest Forms Pro WordPress Plugin Flaw to Take Over Sites
Threat actors are actively exploiting a critical security flaw in Everest Forms Pro, a WordPress plugin with about 4,000 active installations, to execute arbitrary code, leading to a complete site compromise. The vulnerability in question is CVE-2026-3300 (CVSS score: 9.8), a remote code execution bug impacting all versions of the plugin up to, and including, 1.9.12. A patch for the flaw was
- FIFA World Cup 2026 Scams Are Already Live: Fake Sites, Banking Malware, and Stolen Logins
Security researchers and the FBI are warning that a wave of FIFA-themed fraud is already hitting World Cup 2026 fans, days before the June 11 kickoff. Recent reports describe thousands of lookalike FIFA domains, banking malware hidden inside pirate streaming apps, and at least one operation that copies FIFA's login page well enough to take over real accounts. It is an obvious target. More than
- PCPJack Hijacks 230 AWS, Google Cloud, and Azure Servers for Covert SMTP Relay Network
The threat actor known as PCPJack has hijacked cloud servers associated with Amazon Web Services (AWS), Google Cloud, and Microsoft Azure to create a covert SMTP email relay network. "Compromised business servers across the U.S., Europe, and Asia were quietly converted into SMTP proxies, verified for mail relay capability, and synced to a downstream consumer every five minutes," Hunt.io said in
Reduce the Cyber Risk in your Company